
In computing managed security services (MSS) are network security services that have been outsourced to a service provider. A company providing such a service is a managed security service provider (MSSP). The roots of MSSPs are in the Internet Service Providers (ISPs) in the mid-late 1990s. initially, the internet service provider would sell customers a firewall appliance, as customer premises equipment, and for an additional fee would manage the customer-owned firewall over a dial-up connection. Businesses turn to managed security services providers to alleviate the pressures they face daily related to information security such as targeted malware, customer data theft, skills shortages, and resources. Managed security services are also considered the systematic approach to managing an organization’s security needs. The services may be conducted in-house or outsourced to a service provider that oversees other companies’ network and information system security. Functions of a managed security service include round-the-clock monitoring and management of intrusion detection systems and firewalls, overseeing patch management and upgrades, performing security assessments and security audits, and responding to emergencies. The business model behind managed security services is commonplace among large enterprise companies with their IT security experts.
Organizations across sectors are now shifting to managed security services from the traditional in-house IT security practices. A trend of outsourcing IT security jobs to managed security services vendors is picking up at an appreciable pace. This also helps the enterprises to focus more on their core business activities as a strategic approach. Among different prominent players, managed security service provider observes the growing need to combat increasingly complicated and intended attack.
Global Managed Security Services Market – Competitive Landscape
On July 26, 2023, Kyndryl the world’s largest IT infrastructure services provider announced that it has significantly expanded its services up to USD 47 billion, it offers to enable enterprise customers to quickly detect and effectively respond to and recover from cyberattacks. AUcloud nets USD 8.5 million investment to boost cyber security and multi-cloud operation. Netcraft has secured a USD 100 million investment from Spectrum Equity Management.
Some of the Key Players in the Global Managed Security Services Market Include –
Global Managed Security Services Market – Growth Driver
The rise in cyberattacks, including data breaches and ransomware incidents, has driven organizations to seek professional MSS to bolster their cybersecurity defenses. A shortage of skilled cybersecurity professionals has led organizations to outsource their security needs to MSS providers who offer expertise and 24/7 monitoring. Regulatory requirements and data protection laws necessitate robust security measures, prompting companies to invest in MSS for compliance and risk management. The shift to cloud computing has expanded the attack surface, creating a demand for managed security services to secure cloud-based applications and data. The growth of the Internet of Things has increased the number of connected devices, presenting security challenges that MSS providers can address. Outsourcing security to a managed service provider can be cost-effective compared to maintaining an in-house security team and infrastructure. According to the National Center for Biotechnology Information (NCBI), the average cost of managed security service per month is USD 99 to USD 250. Managed security services often integrate with security information and events management systems for comprehensive security monitoring and analysis.
Global Managed Security Services Market – Restraints
Unpatched software may allow an attacker to exploit publicly known vulnerabilities to gain access to sensitive information which takes control of the system. This one is the most commonly found security practice. Use of vendor-supplied default configuration or default login usernames and passwords. Remote services such as a virtual private network, lack sufficient controls to prevent access. Strong password policies are not implemented. Cloud services are unprotected. The cost of MSS can be a barrier for smaller organizations, as it may require a significant investment in cybersecurity services. Some organizations are hesitant to fully rely on MSS providers due to concerns about losing in-house cybersecurity expertise and control. Over-reliance on MSS providers can create a dependency, and if the provider faces issues, it could impact the organization’s security. Managed security services solutions can sometimes generate false positives leading to unnecessary alerts and operational disruptions.
Global Managed Security Services Market – Opportunities
The evolving threat landscape presents opportunities for managed security service providers to offer advanced security solutions to protect organizations against a wide range of cyberattacks. Growing awareness of the importance of cybersecurity is driving demand for managed security services among businesses of all sizes. As organizations embrace digital transformation, there is a need for managed security services to secure cloud-based applications, IoT devices, and other digital assets. The shortage of cybersecurity professionals compels organizations to turn to managed security service providers for expertise and 24/7 monitoring.
Global Managed Security Services Market – Geographical Insight
The market for global managed security services is segmented into regions such as North America, Latin America, Asia-Pacific, Europe, the Middle East, and Africa. The North American region is the largest region due to its large and diverse business landscape, coupled with a high level of cybersecurity awareness, which drives demand for managed security services. Europe has matured the managed security service market, with countries such as the United Kingdom, Germany, and France at the forefront. The Asia-Pacific region is the growing region for managed security service market, led by China, Japan, and India due to rising cyber threats, and government initiatives to enhance cybersecurity have contributed to increased adoption.
Global Managed Security Services Market – Key Development
Research Methodology: Aspects
Market research is a crucial tool for organizations aiming to navigate the dynamic landscape of customer preferences, business trends, and competitive landscapes. At Cognizance Market Research, acknowledging the importance of robust research methodologies is vital to delivering actionable insights to our clientele. The significance of such methodologies lies in their capability to offer clarity in complexity, guiding strategic management with realistic evidence rather than speculation. Our clientele seek insights that excel superficial observations, reaching deep into the details of consumer behaviours, market dynamics, and evolving opportunities. These insights serve as the basis upon which businesses craft tailored approaches, optimize product offerings, and gain a competitive edge in an ever-growing marketplace.
The frequency of information updates is a cornerstone of our commitment to providing timely, relevant, and accurate insights. Cognizance Market Research adheres to a rigorous schedule of data collection, analysis, and distribution to ensure that our reports reflect the most current market realities. This proactive approach enables our clients to stay ahead of the curve, capitalize on emerging trends, and mitigate risks associated with outdated information.
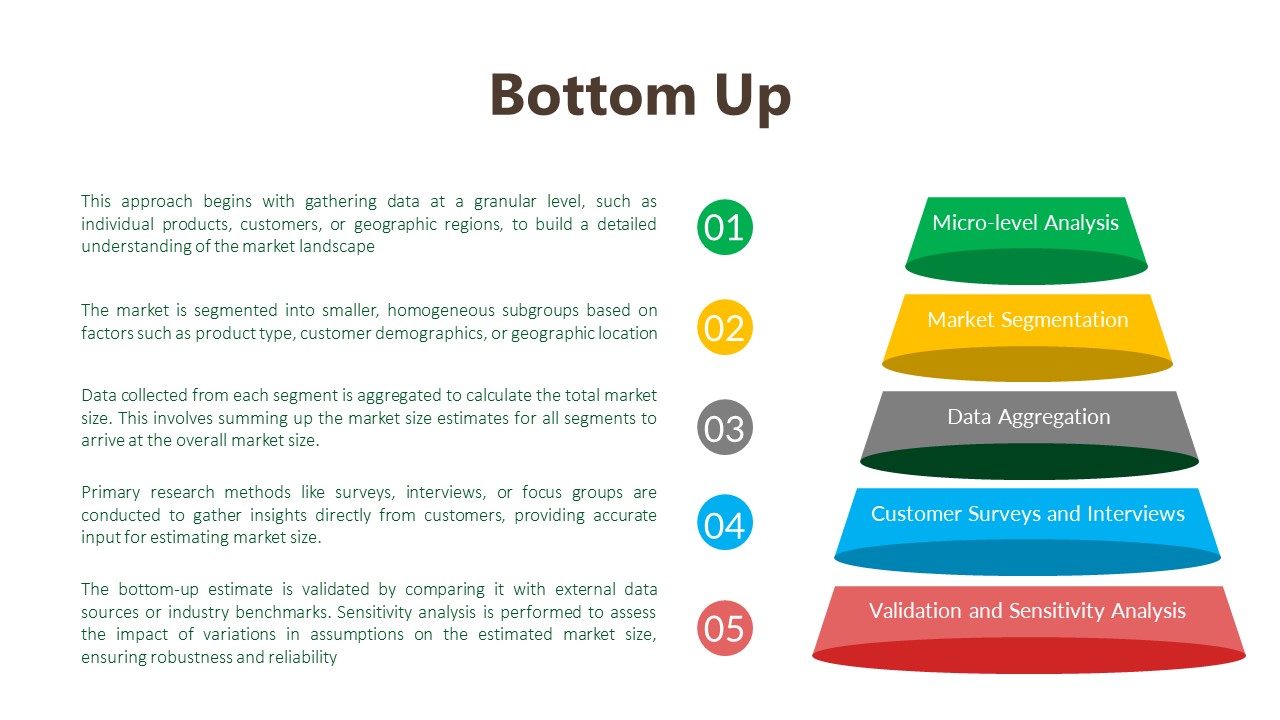
Our research process is characterized by meticulous attention to detail and methodological rigor. It begins with a comprehensive understanding of client objectives, industry dynamics, and research scope. Leveraging a combination of primary and secondary research methodologies, we gather data from diverse sources including surveys, interviews, industry reports, and proprietary databases. Rigorous data analysis techniques are then employed to derive meaningful insights, identify patterns, and uncover actionable recommendations. Throughout the process, we remain vigilant in upholding the highest standards of data integrity, ensuring that our findings are robust, reliable, and actionable.
Key phases involved in in our research process are mentioned below:

Understanding Clients’ Objectives:
Extensive Discussions and Consultations:
Industry and Market Segment Analysis:
Target Audience Understanding:
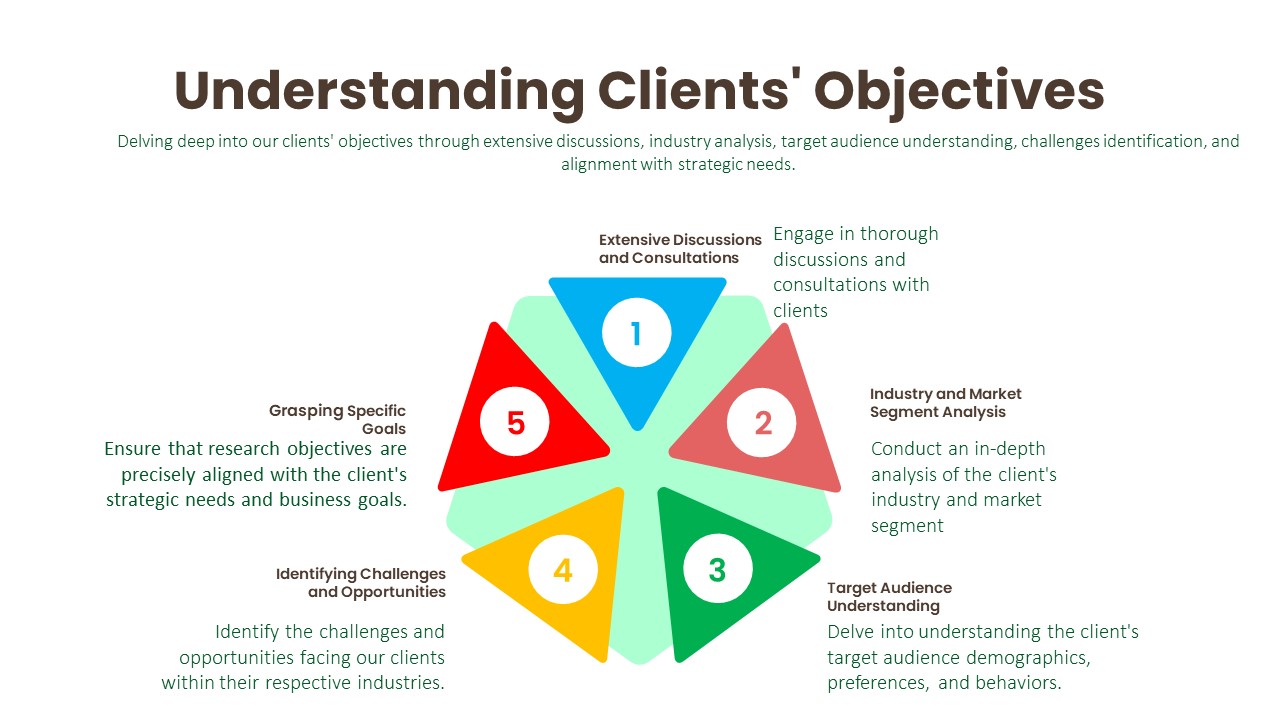
Identifying Challenges and Opportunities:
Grasping Specific Goals:
Data Collection:
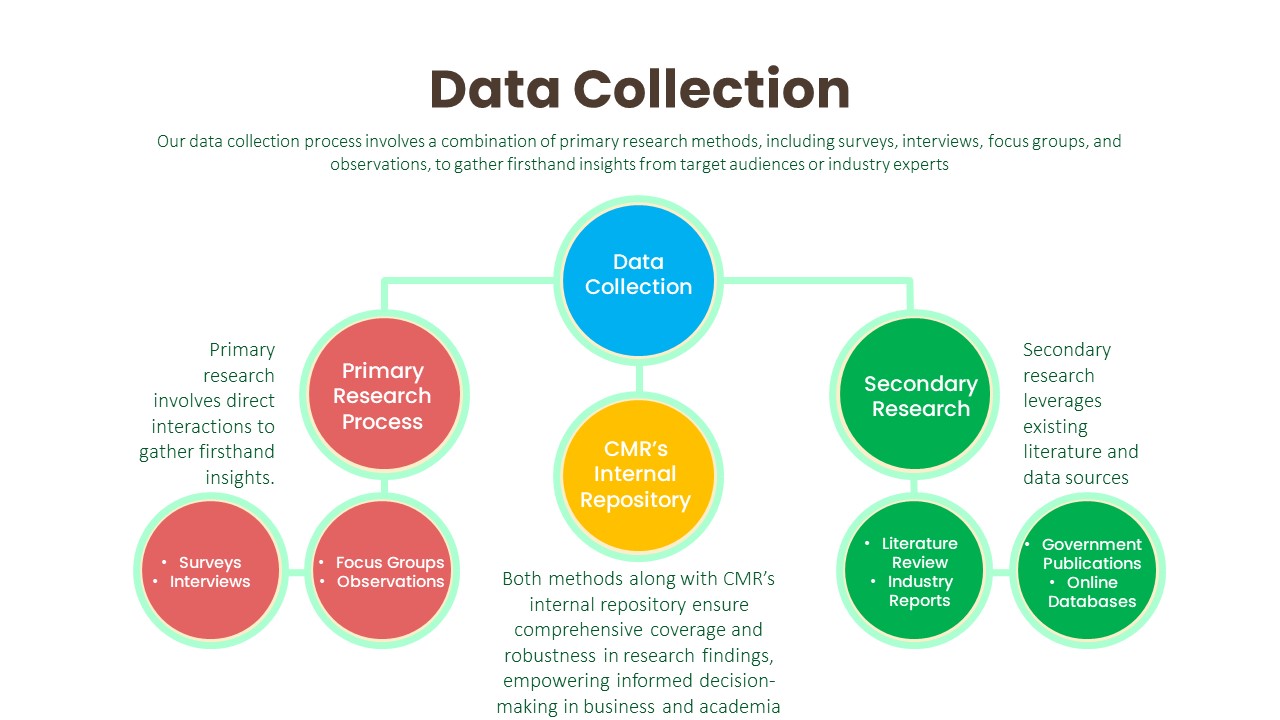
Primary Research Process:
Secondary Research Process:

Data Analysis:
The data analysis phase serves as a critical juncture where raw data is transformed into actionable insights that inform strategic decision-making. Through the utilization of analytical methods such as statistical analysis and qualitative techniques like thematic coding, we uncover patterns, correlations, and trends within the data. By ensuring the integrity and validity of our findings, we strive to provide clients with accurate and reliable insights that accurately reflect the realities of the market landscape.

Transformation of Raw Data:
Utilization of Analytical Methods:
Statistical Analysis:
Qualitative Analysis Techniques:
Integrity and Validity Maintenance:
Data Validation:
The final phase of our research methodology is data validation, which is essential for ensuring the reliability and credibility of our findings. Validation involves scrutinizing the collected data to identify any inconsistencies, errors, or biases that may have crept in during the research process. We employ various validation techniques, including cross-referencing data from multiple sources, conducting validity checks on survey instruments, and seeking feedback from independent experts or peer reviewers. Additionally, we leverage internal quality assurance protocols to verify the accuracy and integrity of our analysis. By subjecting our findings to rigorous validation procedures, we instill confidence in our clients that the insights they receive are robust, reliable, and trustworthy.
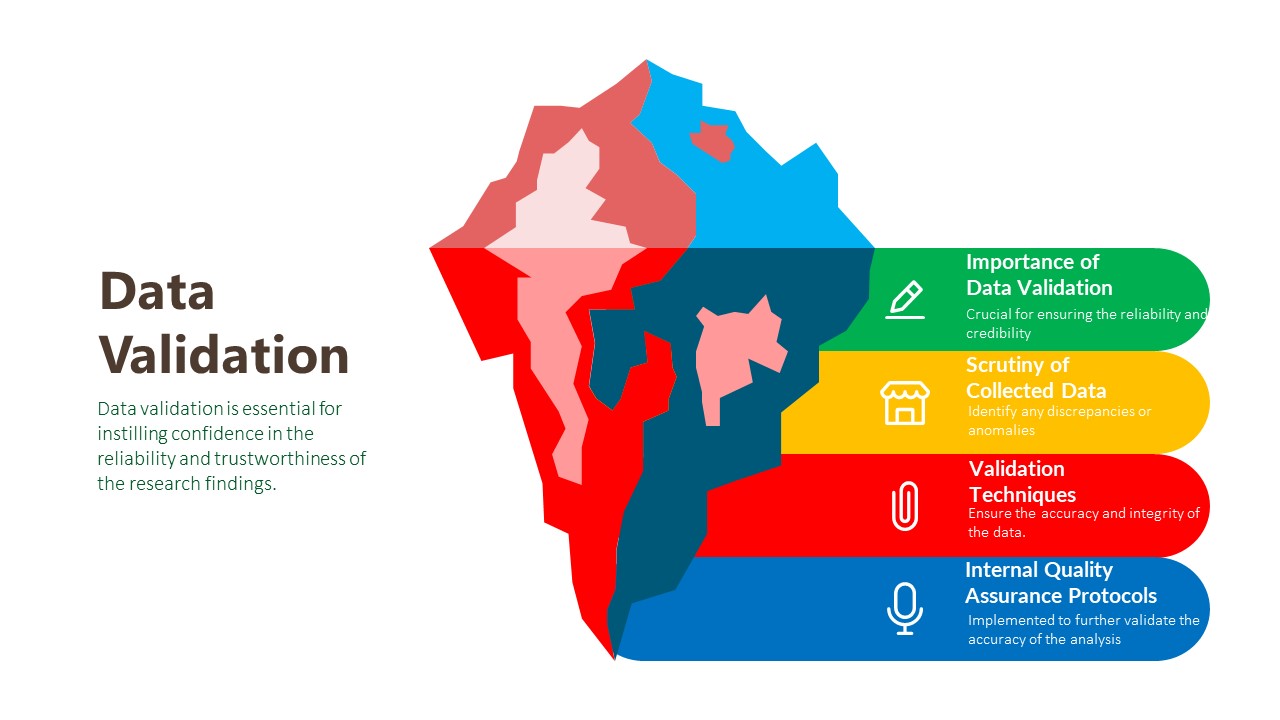
Importance of Data Validation:
Scrutiny of Collected Data:
Validation Techniques:
Internal Quality Assurance Protocols:
We can customize every report – free of charge – including purchasing stand-alone sections or country-level reports
We help clients to procure the report or sections of the report at their budgeted price. Kindly click on the below to avail
Cognizance market research is continuously guiding customers around the globe towards strategies for transformational growth. Today, businesses have to innovate more than ever before, not just to survive, but to succeed in the future

© 2023 All rights Reserved. Cognizance Market Research